In reusable phishing campaigns, attackers don’t bet on a single domain. They build a workflow that can rotate quickly: a bait domain for the click and a more stable hub domain where the content lives and can be reused. When you analyze the case via redirects (not just domain names), the pattern becomes obvious.
What we observed (real example)
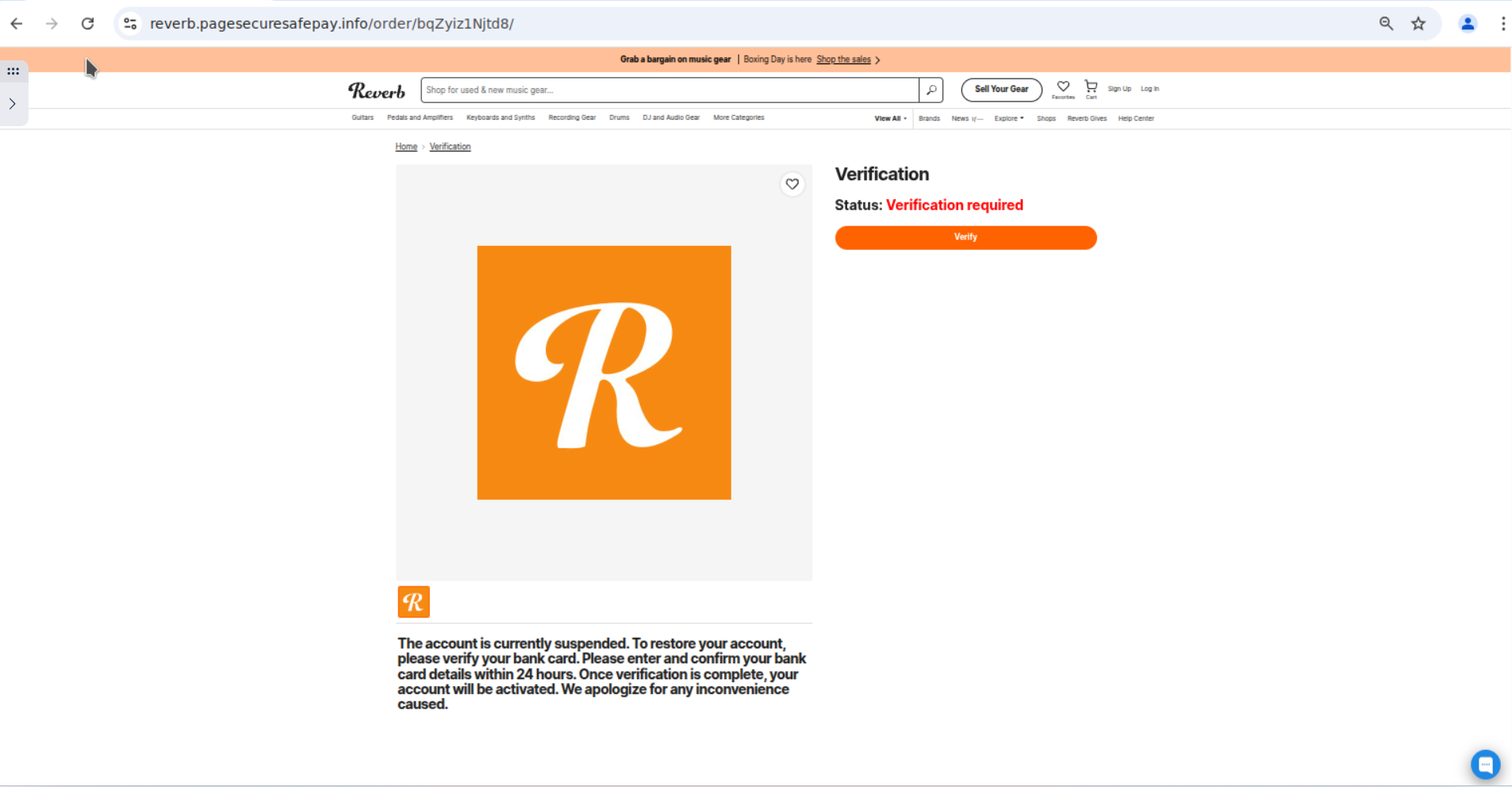
As an example, we observed a bait domain acting as the entry point (reverbverification[.]shop). When accessed, it redirects to a URL hosted under a generic-looking domain:
hxxps://reverb[.]pagesecuresafepay[.]info/
The key is not the specific brand token, but the technique: a brand-token subdomain (<brand>.) inside a generic domain (pagesecuresafepay[.]info) used as a reusable container.
Redirect chain
The observed sequence is simple but effective:
- Entry: the user clicks a bait domain (e.g.,
reverbverification[.]shop). - Jump: the bait redirects to the hub (e.g.,
reverb[.]pagesecuresafepay[.]info). - Landing: content stays under the generic domain; attackers can create new subdomains for other brands/campaigns.
If your detection only tracks bait (lookalike) domains, you’ll see domains that quickly rotate. Following redirects and spotting generic hubs helps uncover reusable infrastructure that repeats across campaigns.
The problem: hubs on generic domains
This pattern is designed to scale. The generic domain acts as the attacker’s platform, and brand-token subdomains act as per-campaign templates. Common operational advantages:
- Reuse: one generic domain can host multiple campaigns (one per subdomain).
- Fast rotation: if the bait domain gets blocked, a new one can be registered and pointed to the same hub.
- User confusion: many users focus on the brand token at the start (
<brand>.), not the registrable domain. - Economies of scale: less effort to deploy and maintain infrastructure.
Detection beyond lookalike domains
From day one, our concern hasn’t been limited to domains: subdomains matter just as much. In modern campaigns, subdomains are where attackers inject the brand token and pivot to reuse infrastructure at scale. That reality has shaped how our detection engine and modules have been built.
In reusable campaigns, the subdomain is where attackers “personalize” impersonation while keeping the base domain as the hub.
Notmining Platform is built to cover both sides of the problem:
- Lookalike monitoring: detect new registrations and activity tied to brand tokens, variants, and high-risk terms (verify, secure, login, support, etc.).
- Subdomain-focused detection: modules like Zero Scam, Zero Scam SSL and Generic Phishing include subdomain detection in addition to domain detection, because subdomains are often the impersonation layer inside reusable infrastructure.
- Generic phishing: in addition to brands, we monitor generic-term domains attackers reuse as campaign containers.
- Subdomain discovery: on those generic domains, we perform active subdomain discovery by testing user-configured words (brand/product terms) combined with the generic domain. This helps surface
<brand>.<generic-domain>patterns without relying on external reports. - Content similarity: detection via structural and content signals to identify reusable landings and kits even when domains rotate.
- Change monitoring: when an asset is added to monitoring, we alert on relevant changes affecting the monitored domain, including the appearance of new subdomains.
In practice, this increases coverage and reduces blind spots when attackers split bait domains from reusable infrastructure.
Indicators (IOCs)
Observed indicators in this example:
- Bait domain:
reverbverification[.]shop - Destination (landing):
reverb[.]pagesecuresafepay[.]info
Detection tip: record and correlate redirects from lookalike domains to generic domains. When a destination repeats, it often signals infrastructure reuse.
Quick recommendations
- Layered blocking: block both the bait and destination domains at DNS, proxy, and web filtering layers.
- Redirect hunting: review HTTP logs for other domains redirecting to
*[.]pagesecuresafepay[.]info. - Response: pursue takedown both via hosting (content) and registrar (domain), prioritizing the generic hub if reuse is confirmed.
- Prevention: strengthen user guidance and MFA, assuming credential theft is the goal.
Key takeaways
- The domain users click is not always where the campaign lives.
- Generic domains with brand-like subdomains enable reusable, multi-brand phishing infrastructure.
- Combining lookalike monitoring with generic phishing and subdomain discovery reduces blind spots.
- Operationally, identifying and removing the reusable hub is often the priority.